
The Apperta Foundation had public code on GitHub stuffed full of secrets.
A week later I hear from Apperta's lawyers.
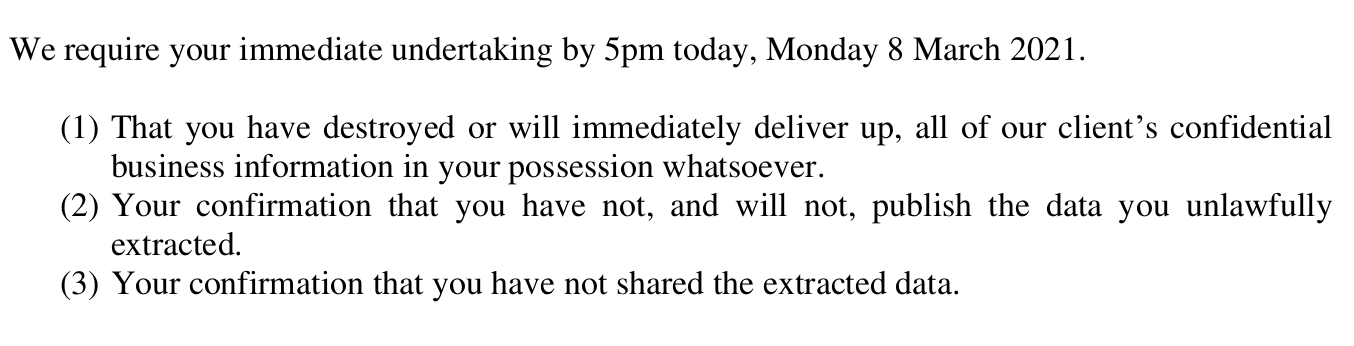
We require your immediate undertaking by 5pm today, Monday 8 March 2021. That you have destroyed or will immediately deliver up, all of our client’s confidential business information in your possession whatsoever. Your confirmation that you have not, and will not, publish the data you unlawfully extracted. Your confirmation that you have not shared the extracted data.
Don't shoot the messenger.
On or around October 30th 2019 your client published two repositories of code on the public code sharing website Github. These materials were freely available for anyone to view clone fork or download from that date.
Thank you for making me aware that your client considers the data that they purposefully published on Github in 2019 as private and confidential business information. I trust that they will be notifying the ICO of the data breach.
An unacceptable undertalking.
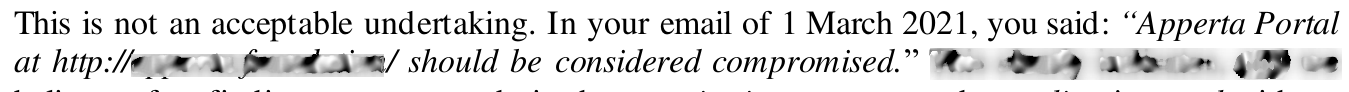
Since we wrote earlier today, it has now come to our attention that you have boasted of your unlawful extraction and also today threatened to unlawfully access our client’s systems and data again.

Rob Dyke
@robdykedotcom
Found a public repo with API keys, usernames,
passwords, and a database dump.
Notified owners.
Gone
now.

Rob Dyke
@robdykedotcom
I am 100% behind this from
@ThatPodcastChap
"Take responsibility or be hacked again."
ESPECIALLY relevant for companies in the open source world.
I suspect the first headline was 'Grow a pair or piss off')
Our client has a real belief that you pose an imminent further threat and that you now retain its confidential business information and data. You have failed to provide the undertaking requested. Please advise how we may serve your solicitor. If you are representing yourself, kindly confirm.
Next...
2
Public repos with secret info
500+
Emails between lawyers
£25k
Costs & Legal fees
8
Confirmations / undertakings offered
3
High Court forms
£15k
Go Fund Me Donations (after fees)
5
Press interviews
+1k
Twitter followers
1
Confirmation / undertaking accepted
2
weeks off sick from stress
£5k
Own savings
177
Pages in court bundle